As cyberthreats evolve and federal data environments grow increasingly complex, agencies face mounting challenges in securing access to sensitive information across multiple domains. Whether within the Department of Defense (DoD) or civilian branches, maintaining both usability and airtight security is paramount. Secure KVM switches play a vital role in this mission by enabling users to access multiple computers — each operating at different classification levels — from a single workstation, all while maintaining strict data separation. Secure KVM technology enhances cybersecurity, improves workflows, and supports compliance across diverse government environments.
Secure KVM switches are hardware-based devices that let one keyboard, monitor, and mouse control multiple systems securely — without compromising classified or sensitive data. Unlike standard KVMs, NIAP-certified secure KVMs are designed specifically for high-security environments, where the risk of data leakage between networks must be mitigated. These switches are often deployed in multi-domain settings, where users may need to access unclassified, classified, secret, or top-secret systems from a single location.
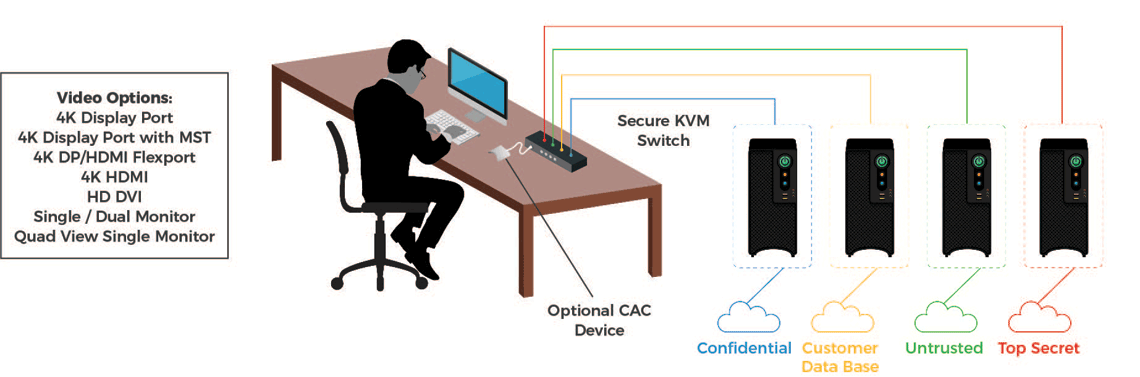
The illustration below shows a sample separation of network access:
The cybersecurity benefits of secure KVM switches are substantial. First, they provide complete data isolation, physically and electronically separating networks to prevent cross-domain contamination. NIAP Protection Profile v4.0 certification ensures that the device meets the highest federal cybersecurity standards, with many models also offering FIPS 140-2 validated encryption and TEMPEST shielding for environments requiring electromagnetic emission control. Hardware-based unidirectional data flow — often referred to as data diode functionality — ensures that data only moves in one direction, eliminating backflow and minimizing the risk of I/O compromise. Additionally, secure KVMs help prevent insider threats by locking down USB access and peripheral connectivity, significantly reducing the attack surface for malware or data exfiltration.
From the end user’s perspective, secure KVMs offer unmatched workflow efficiency. Operators can switch instantly between systems at different security levels without logging in and out or changing physical workstations. This saves time, improves response speed, and reduces desk clutter, especially in space-constrained or high-activity environments like security operations centers. Because secure KVMs operate independently of any OS or installed software, they’re ideal for zero trust architectures, providing security without adding a software footprint.
For Department of Defense agencies, secure KVM switches support Multi-Level Security (MLS) by enabling simultaneous access to networks like NIPRNet, SIPRNet, and JWICS. Their reliability makes them ideal for mission continuity in field operations and tactical deployments. Many DoD-compliant models also offer TEMPEST or NATO shielding, making them suitable for the most sensitive global operations. In joint military environments, secure KVMs facilitate collaboration between service branches while keeping data domains securely separated.
Civilian agencies also benefit from secure KVMs in environments that require varying levels of access clearance. As agencies modernize and adopt hybrid work environments, secure KVMs support secure remote access without exposing internal networks. With compliance mandates like FISMA, NIST SP 800-53, and agency-specific guidelines, secure KVMs help ensure that data remains protected and user access is tightly controlled. Because these solutions consolidate multiple systems into one interface, they also offer long-term cost efficiency, especially in public-facing environments that handle sensitive citizen data.
When selecting a secure KVM solution, federal IT decision-makers should evaluate key features: the number of ports needed (2, 4, 8, or more), support for Common Access Cards (CAC), audio isolation, and physical security features like tamper-evident seals or locked-down firmware. Always verify products against the NIAP Product Compliant List (PCL) and choose TAA-compliant vendors to meet federal procurement requirements. These devices are widely available through trusted channels like GSA, NASA SEWP, and other federal contract vehicles.
Secure KVM switches are far more than convenience tools — they’re essential to protecting national security assets, maintaining operational efficiency, and ensuring compliance across all levels of government. Whether supporting critical defense operations or enhancing cybersecurity posture in civilian agencies, secure KVMs offer a scalable, reliable, and certifiable foundation for information assurance. To get started, contact our solutions experts today.
Learn more about our secure KVM solutions here.
Check out a few related blogs:
Blog: Protect Your Network: NIAP 4.0 Explained
Blog: NIAP 3.0 vs. NIAP 4.0: What’s the Difference?
Blog: Beyond Cybersecurity: What Is Information Assurance?
For a more detailed analysis of cybersecurity best practices, download our white paper:
White Paper: Cybersecurity in Critical Control Rooms